Open source software is an important cornerstone to the HPC community, spanning all layers from the operating systems, middlewares, and actual applications. But the very intentionally open dynamic of open source communities make them also vulnerable to malicious actors.
In this case a group of researchers submitted a paper to the 42nd IEEE Symposium on Security and Privacy, for which they introduced small bugs to the Linux kernel to see if they would pass the review process. While the general threat model seems plausible and understanding the dynamics to finding potential mitigations worthwhile, the methodology also raises a number of ethical concerns. It has also raised controversy in the kernel developer community, leading to at least a temporary ban of all submissions from the University of Minnesota, along with a review looking to revert many changes earlier
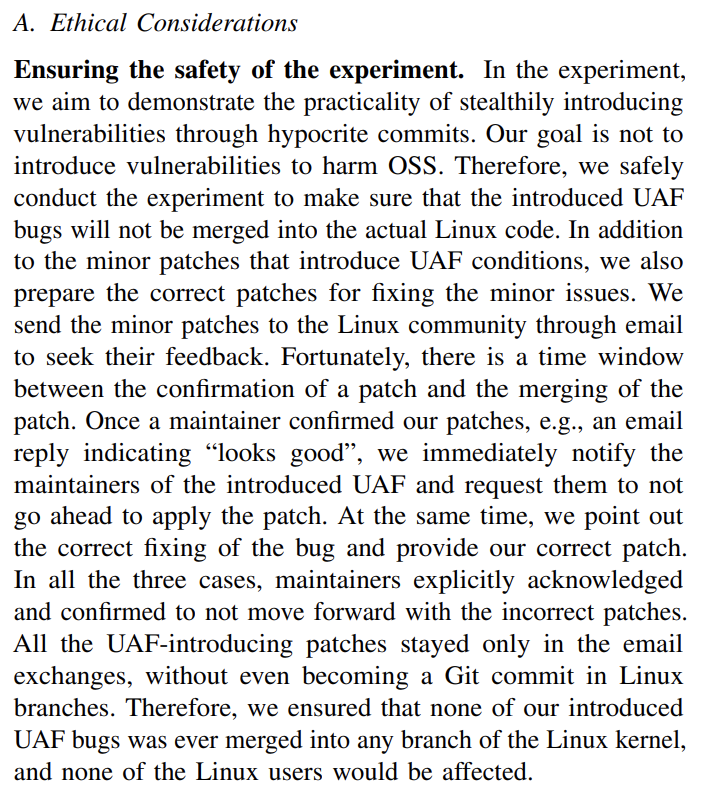
Now the researchers were aware of potential ethical problems of their research and also discussed how to ensure that no vulnerabilities would actually be merged. At the same time the ethical dimension of potentially wasting the time of volunteers and maintainers was overlooked.
The Department of Computer Science & Engineering has since issued a statement to investigate the research method and the process by which the research method was approved, and also determine appropriate remedial action and safeguards to prevent similar issues in the future.
{295846:K6E7BFQ6};{295846:HXXMPUBW}
apa
default
0
696
%7B%22status%22%3A%22success%22%2C%22updateneeded%22%3Afalse%2C%22instance%22%3Afalse%2C%22meta%22%3A%7B%22request_last%22%3A0%2C%22request_next%22%3A0%2C%22used_cache%22%3Atrue%7D%2C%22data%22%3A%5B%7B%22key%22%3A%22DJVBQQ7Y%22%2C%22library%22%3A%7B%22id%22%3A295846%7D%2C%22meta%22%3A%7B%22creatorSummary%22%3A%22Heath%22%2C%22parsedDate%22%3A%222018%22%2C%22numChildren%22%3A1%7D%2C%22bib%22%3A%22%26lt%3Bdiv%20class%3D%26quot%3Bcsl-bib-body%26quot%3B%20style%3D%26quot%3Bline-height%3A%202%3B%20padding-left%3A%202em%3B%20text-indent%3A-2em%3B%26quot%3B%26gt%3B%5Cn%20%20%26lt%3Bdiv%20class%3D%26quot%3Bcsl-entry%26quot%3B%26gt%3BHeath%2C%20N.%20%282018%29.%20NASA%26%23x2019%3Bs%20unsung%20heroes%3A%20The%20Apollo%20coders%20who%20put%20men%20on%20the%20moon.%20Retrieved%20November%2013%2C%202019%2C%20from%20%26lt%3Ba%20class%3D%26%23039%3Bzp-ItemURL%26%23039%3B%20href%3D%26%23039%3Bhttps%3A%5C%2F%5C%2Fwww.techrepublic.com%5C%2Farticle%5C%2Fnasas-unsung-heroes-the-apollo-coders-who-put-men-on-the-moon%5C%2F%26%23039%3B%26gt%3Bhttps%3A%5C%2F%5C%2Fwww.techrepublic.com%5C%2Farticle%5C%2Fnasas-unsung-heroes-the-apollo-coders-who-put-men-on-the-moon%5C%2F%26lt%3B%5C%2Fa%26gt%3B%26lt%3B%5C%2Fdiv%26gt%3B%5Cn%26lt%3B%5C%2Fdiv%26gt%3B%22%2C%22data%22%3A%7B%22itemType%22%3A%22webpage%22%2C%22title%22%3A%22NASA%27s%20unsung%20heroes%3A%20The%20Apollo%20coders%20who%20put%20men%20on%20the%20moon%22%2C%22creators%22%3A%5B%7B%22creatorType%22%3A%22author%22%2C%22firstName%22%3A%22Nick%22%2C%22lastName%22%3A%22Heath%22%7D%5D%2C%22abstractNote%22%3A%22Learn%20how%20pioneering%20software%20engineers%20helped%20NASA%20launch%20astronauts%20into%20space%2C%20and%20bring%20them%20back%20again--pushing%20the%20boundaries%20of%20technology%20as%20they%20did%20it.%22%2C%22date%22%3A%222018%22%2C%22url%22%3A%22https%3A%5C%2F%5C%2Fwww.techrepublic.com%5C%2Farticle%5C%2Fnasas-unsung-heroes-the-apollo-coders-who-put-men-on-the-moon%5C%2F%22%2C%22language%22%3A%22en%22%2C%22collections%22%3A%5B%22P6DD6IKL%22%5D%2C%22dateModified%22%3A%222020-07-22T10%3A51%3A45Z%22%7D%7D%2C%7B%22key%22%3A%22DV2Z98A9%22%2C%22library%22%3A%7B%22id%22%3A295846%7D%2C%22meta%22%3A%7B%22creatorSummary%22%3A%22Nirkin%20et%20al.%22%2C%22parsedDate%22%3A%222019-08-16%22%2C%22numChildren%22%3A3%7D%2C%22bib%22%3A%22%26lt%3Bdiv%20class%3D%26quot%3Bcsl-bib-body%26quot%3B%20style%3D%26quot%3Bline-height%3A%202%3B%20padding-left%3A%202em%3B%20text-indent%3A-2em%3B%26quot%3B%26gt%3B%5Cn%20%20%26lt%3Bdiv%20class%3D%26quot%3Bcsl-entry%26quot%3B%26gt%3BNirkin%2C%20Y.%2C%20Keller%2C%20Y.%2C%20%26amp%3B%20Hassner%2C%20T.%20%282019%29.%20FSGAN%3A%20Subject%20Agnostic%20Face%20Swapping%20and%20Reenactment.%20%26lt%3Bi%26gt%3BArXiv%3A1908.05932%20%5BCs%5D%26lt%3B%5C%2Fi%26gt%3B.%20Retrieved%20from%20%26lt%3Ba%20class%3D%26%23039%3Bzp-ItemURL%26%23039%3B%20href%3D%26%23039%3Bhttp%3A%5C%2F%5C%2Farxiv.org%5C%2Fabs%5C%2F1908.05932%26%23039%3B%26gt%3Bhttp%3A%5C%2F%5C%2Farxiv.org%5C%2Fabs%5C%2F1908.05932%26lt%3B%5C%2Fa%26gt%3B%26lt%3B%5C%2Fdiv%26gt%3B%5Cn%26lt%3B%5C%2Fdiv%26gt%3B%22%2C%22data%22%3A%7B%22itemType%22%3A%22journalArticle%22%2C%22title%22%3A%22FSGAN%3A%20Subject%20Agnostic%20Face%20Swapping%20and%20Reenactment%22%2C%22creators%22%3A%5B%7B%22creatorType%22%3A%22author%22%2C%22firstName%22%3A%22Yuval%22%2C%22lastName%22%3A%22Nirkin%22%7D%2C%7B%22creatorType%22%3A%22author%22%2C%22firstName%22%3A%22Yosi%22%2C%22lastName%22%3A%22Keller%22%7D%2C%7B%22creatorType%22%3A%22author%22%2C%22firstName%22%3A%22Tal%22%2C%22lastName%22%3A%22Hassner%22%7D%5D%2C%22abstractNote%22%3A%22We%20present%20Face%20Swapping%20GAN%20%28FSGAN%29%20for%20face%20swapping%20and%20reenactment.%20Unlike%20previous%20work%2C%20FSGAN%20is%20subject%20agnostic%20and%20can%20be%20applied%20to%20pairs%20of%20faces%20without%20requiring%20training%20on%20those%20faces.%20To%20this%20end%2C%20we%20describe%20a%20number%20of%20technical%20contributions.%20We%20derive%20a%20novel%20recurrent%20neural%20network%20%28RNN%29-based%20approach%20for%20face%20reenactment%20which%20adjusts%20for%20both%20pose%20and%20expression%20variations%20and%20can%20be%20applied%20to%20a%20single%20image%20or%20a%20video%20sequence.%20For%20video%20sequences%2C%20we%20introduce%20continuous%20interpolation%20of%20the%20face%20views%20based%20on%20reenactment%2C%20Delaunay%20Triangulation%2C%20and%20barycentric%20coordinates.%20Occluded%20face%20regions%20are%20handled%20by%20a%20face%20completion%20network.%20Finally%2C%20we%20use%20a%20face%20blending%20network%20for%20seamless%20blending%20of%20the%20two%20faces%20while%20preserving%20target%20skin%20color%20and%20lighting%20conditions.%20This%20network%20uses%20a%20novel%20Poisson%20blending%20loss%20which%20combines%20Poisson%20optimization%20with%20perceptual%20loss.%20We%20compare%20our%20approach%20to%20existing%20state-of-the-art%20systems%20and%20show%20our%20results%20to%20be%20both%20qualitatively%20and%20quantitatively%20superior.%22%2C%22date%22%3A%222019-08-16%22%2C%22language%22%3A%22%22%2C%22DOI%22%3A%22%22%2C%22ISSN%22%3A%22%22%2C%22url%22%3A%22http%3A%5C%2F%5C%2Farxiv.org%5C%2Fabs%5C%2F1908.05932%22%2C%22collections%22%3A%5B%224VTX49XL%22%5D%2C%22dateModified%22%3A%222020-07-22T10%3A49%3A18Z%22%7D%7D%2C%7B%22key%22%3A%22NVC3JTWT%22%2C%22library%22%3A%7B%22id%22%3A295846%7D%2C%22meta%22%3A%7B%22creatorSummary%22%3A%22K%5Cu00e1roly%20Zsolnai-Feh%5Cu00e9r%22%2C%22parsedDate%22%3A%222019%22%2C%22numChildren%22%3A0%7D%2C%22bib%22%3A%22%26lt%3Bdiv%20class%3D%26quot%3Bcsl-bib-body%26quot%3B%20style%3D%26quot%3Bline-height%3A%202%3B%20padding-left%3A%202em%3B%20text-indent%3A-2em%3B%26quot%3B%26gt%3B%5Cn%20%20%26lt%3Bdiv%20class%3D%26quot%3Bcsl-entry%26quot%3B%26gt%3BK%26%23xE1%3Broly%20Zsolnai-Feh%26%23xE9%3Br.%20%282019%29.%20%26lt%3Bi%26gt%3BDeepFake%20Detector%20AIs%20Are%20Good%20Too%21%26lt%3B%5C%2Fi%26gt%3B%20Retrieved%20from%20%26lt%3Ba%20class%3D%26%23039%3Bzp-ItemURL%26%23039%3B%20href%3D%26%23039%3Bhttps%3A%5C%2F%5C%2Fwww.youtube.com%5C%2Fwatch%3Fv%3DRoGHVI-w9bE%26%23039%3B%26gt%3Bhttps%3A%5C%2F%5C%2Fwww.youtube.com%5C%2Fwatch%3Fv%3DRoGHVI-w9bE%26lt%3B%5C%2Fa%26gt%3B%26lt%3B%5C%2Fdiv%26gt%3B%5Cn%26lt%3B%5C%2Fdiv%26gt%3B%22%2C%22data%22%3A%7B%22itemType%22%3A%22videoRecording%22%2C%22title%22%3A%22DeepFake%20Detector%20AIs%20Are%20Good%20Too%21%22%2C%22creators%22%3A%5B%7B%22creatorType%22%3A%22director%22%2C%22name%22%3A%22K%5Cu00e1roly%20Zsolnai-Feh%5Cu00e9r%22%7D%5D%2C%22abstractNote%22%3A%22%5Cu2764%5Cufe0f%20Pick%20up%20cool%20perks%20on%20our%20Patreon%20page%3A%20https%3A%5C%2F%5C%2Fwww.patreon.com%5C%2FTwoMinutePapers%5Cn%5Cn%5Cud83d%5Cudcdd%20The%20paper%20%26quot%3BFaceForensics%2B%2B%3A%20Learning%20to%20Detect%20Manipulated%20Facial%20Images%26quot%3B%20is%20available%20here%3A%5Cnhttp%3A%5C%2F%5C%2Fwww.niessnerlab.org%5C%2Fprojects%5C%2Fr...%5Cn%5Cn%5Cud83d%5Cude4f%20We%20would%20like%20to%20thank%20our%20generous%20Patreon%20supporters%20who%20make%20Two%20Minute%20Papers%20possible%3A%5CnAlex%20Haro%2C%20Andrew%20Melnychuk%2C%20Angelos%20Evripiotis%2C%20Anthony%20Vdovitchenko%2C%20Brian%20Gilman%2C%20Bryan%20Learn%2C%20Christian%20Ahlin%2C%20Claudio%20Fernandes%2C%20Daniel%20Hasegan%2C%20Dennis%20Abts%2C%20Eric%20Haddad%2C%20Eric%20Martel%2C%20Evan%20Breznyik%2C%20Geronimo%20Moralez%2C%20James%20Watt%2C%20Javier%20Bustamante%2C%20John%20De%20Witt%2C%20Kaiesh%20Vohra%2C%20Kasia%20Hayden%2C%20Kjartan%20Olason%2C%20Levente%20Szabo%2C%20Lorin%20Atzberger%2C%20Lukas%20Biewald%2C%20Marcin%20Dukaczewski%2C%20Marten%20Rauschenberg%2C%20Matthias%20Jost%2C%2C%20Maurits%20van%20Mastrigt%2C%20Michael%20Albrecht%2C%20Michael%20Jensen%2C%20Nader%20Shakerin%2C%20Owen%20Campbell-Moore%2C%20Owen%20Skarpness%2C%20Raul%20Ara%5Cu00fajo%20da%20Silva%2C%20Rob%20Rowe%2C%20Robin%20Graham%2C%20Ryan%20Monsurate%2C%20Shawn%20Azman%2C%20Steef%2C%20Steve%20Messina%2C%20Sunil%20Kim%2C%20Taras%20Bobrovytsky%2C%20Thomas%20Krcmar%2C%20Torsten%20Reil.%5Cnhttps%3A%5C%2F%5C%2Fwww.patreon.com%5C%2FTwoMinutePapers%5Cn%5CnSplash%20screen%5C%2Fthumbnail%20design%3A%20Fel%5Cu00edcia%20Feh%5Cu00e9r%20-%20http%3A%5C%2F%5C%2Ffelicia.hu%5Cn%5CnK%5Cu00e1roly%20Zsolnai-Feh%5Cu00e9r%26%23039%3Bs%20links%3A%5CnInstagram%3A%20https%3A%5C%2F%5C%2Fwww.instagram.com%5C%2Ftwominutepa...%5CnTwitter%3A%20https%3A%5C%2F%5C%2Ftwitter.com%5C%2Fkaroly_zsolnai%5CnWeb%3A%20https%3A%5C%2F%5C%2Fcg.tuwien.ac.at%5C%2F~zsolnai%5C%2F%5Cn%5Cn%23DeepFake%20%23DeepFakes%20%23FaceSwap%22%2C%22videoRecordingFormat%22%3A%22%22%2C%22studio%22%3A%22%22%2C%22date%22%3A%222019%22%2C%22runningTime%22%3A%225%3A03%22%2C%22language%22%3A%22%22%2C%22ISBN%22%3A%22%22%2C%22url%22%3A%22https%3A%5C%2F%5C%2Fwww.youtube.com%5C%2Fwatch%3Fv%3DRoGHVI-w9bE%22%2C%22collections%22%3A%5B%224VTX49XL%22%5D%2C%22dateModified%22%3A%222020-07-22T10%3A48%3A30Z%22%7D%7D%2C%7B%22key%22%3A%222M48J9KI%22%2C%22library%22%3A%7B%22id%22%3A295846%7D%2C%22meta%22%3A%7B%22numChildren%22%3A0%7D%2C%22bib%22%3A%22%26lt%3Bdiv%20class%3D%26quot%3Bcsl-bib-body%26quot%3B%20style%3D%26quot%3Bline-height%3A%202%3B%20padding-left%3A%202em%3B%20text-indent%3A-2em%3B%26quot%3B%26gt%3B%5Cn%20%20%26lt%3Bdiv%20class%3D%26quot%3Bcsl-entry%26quot%3B%26gt%3B%26lt%3Bi%26gt%3BNew%20Face%20Swapping%20AI%20Creates%20Amazing%20DeepFakes%26lt%3B%5C%2Fi%26gt%3B.%20%28n.d.%29.%20Retrieved%20from%20%26lt%3Ba%20class%3D%26%23039%3Bzp-ItemURL%26%23039%3B%20href%3D%26%23039%3Bhttps%3A%5C%2F%5C%2Fwww.youtube.com%5C%2Fwatch%3Fv%3Dduo-tHbSdMk%26%23039%3B%26gt%3Bhttps%3A%5C%2F%5C%2Fwww.youtube.com%5C%2Fwatch%3Fv%3Dduo-tHbSdMk%26lt%3B%5C%2Fa%26gt%3B%26lt%3B%5C%2Fdiv%26gt%3B%5Cn%26lt%3B%5C%2Fdiv%26gt%3B%22%2C%22data%22%3A%7B%22itemType%22%3A%22videoRecording%22%2C%22title%22%3A%22New%20Face%20Swapping%20AI%20Creates%20Amazing%20DeepFakes%22%2C%22creators%22%3A%5B%5D%2C%22abstractNote%22%3A%22%5Cud83d%5Cudcdd%20The%20paper%20%26quot%3BFSGAN%3A%20Subject%20Agnostic%20Face%20Swapping%20and%20Reenactment%26quot%3B%20is%20available%20here%3A%5Cnhttps%3A%5C%2F%5C%2Fnirkin.com%5C%2Ffsgan%5C%2F%5Cn%5Cn%5Cu2764%5Cufe0f%20Pick%20up%20cool%20perks%20on%20our%20Patreon%20page%3A%20https%3A%5C%2F%5C%2Fwww.patreon.com%5C%2FTwoMinutePapers%5Cn%5Cn%5Cud83d%5Cude4f%20We%20would%20like%20to%20thank%20our%20generous%20Patreon%20supporters%20who%20make%20Two%20Minute%20Papers%20possible%3A%5CnAlex%20Haro%2C%20Andrew%20Melnychuk%2C%20Angelos%20Evripiotis%2C%20Anthony%20Vdovitchenko%2C%20Brian%20Gilman%2C%20Bruno%20Brito%2C%20Bryan%20Learn%2C%20Christian%20Ahlin%2C%20Christoph%20Jadanowski%2C%20Claudio%20Fernandes%2C%20Daniel%20Hasegan%2C%20Dennis%20Abts%2C%20Eric%20Haddad%2C%20Eric%20Martel%2C%20Evan%20Breznyik%2C%20Geronimo%20Moralez%2C%20James%20Watt%2C%20Javier%20Bustamante%2C%20John%20De%20Witt%2C%20Kaiesh%20Vohra%2C%20Kasia%20Hayden%2C%20Kjartan%20Olason%2C%20Levente%20Szabo%2C%20Lorin%20Atzberger%2C%20Lukas%20Biewald%2C%20Marcin%20Dukaczewski%2C%20Marten%20Rauschenberg%2C%20Matthias%20Jost%2C%2C%20Maurits%20van%20Mastrigt%2C%20Michael%20Albrecht%2C%20Michael%20Jensen%2C%20Nader%20Shakerin%2C%20Owen%20Campbell-Moore%2C%20Owen%20Skarpness%2C%20Raul%20Ara%5Cu00fajo%20da%20Silva%2C%20Rob%20Rowe%2C%20Robin%20Graham%2C%20Ryan%20Monsurate%2C%20Shawn%20Azman%2C%20Steef%2C%20Steve%20Messina%2C%20Sunil%20Kim%2C%20Taras%20Bobrovytsky%2C%20Thomas%20Krcmar%2C%20Torsten%20Reil.%5Cnhttps%3A%5C%2F%5C%2Fwww.patreon.com%5C%2FTwoMinutePapers%5Cn%5CnSplash%20screen%5C%2Fthumbnail%20design%3A%20Fel%5Cu00edcia%20Feh%5Cu00e9r%20-%20http%3A%5C%2F%5C%2Ffelicia.hu%5Cn%5CnK%5Cu00e1roly%20Zsolnai-Feh%5Cu00e9r%26%23039%3Bs%20links%3A%5CnInstagram%3A%20https%3A%5C%2F%5C%2Fwww.instagram.com%5C%2Ftwominutepa...%5CnTwitter%3A%20https%3A%5C%2F%5C%2Ftwitter.com%5C%2Fkaroly_zsolnai%5CnWeb%3A%20https%3A%5C%2F%5C%2Fcg.tuwien.ac.at%5C%2F~zsolnai%5C%2F%5Cn%5Cn%23DeepFakes%20%23FaceSwap%22%2C%22videoRecordingFormat%22%3A%22%22%2C%22studio%22%3A%22%22%2C%22date%22%3A%22%22%2C%22runningTime%22%3A%224%3A12%22%2C%22language%22%3A%22%22%2C%22ISBN%22%3A%22%22%2C%22url%22%3A%22https%3A%5C%2F%5C%2Fwww.youtube.com%5C%2Fwatch%3Fv%3Dduo-tHbSdMk%22%2C%22collections%22%3A%5B%224VTX49XL%22%5D%2C%22dateModified%22%3A%222020-07-22T08%3A27%3A31Z%22%7D%7D%2C%7B%22key%22%3A%22MNDVZ7BZ%22%2C%22library%22%3A%7B%22id%22%3A295846%7D%2C%22meta%22%3A%7B%22numChildren%22%3A0%7D%2C%22bib%22%3A%22%26lt%3Bdiv%20class%3D%26quot%3Bcsl-bib-body%26quot%3B%20style%3D%26quot%3Bline-height%3A%202%3B%20padding-left%3A%202em%3B%20text-indent%3A-2em%3B%26quot%3B%26gt%3B%5Cn%20%20%26lt%3Bdiv%20class%3D%26quot%3Bcsl-entry%26quot%3B%26gt%3B%26lt%3Bi%26gt%3BNVIDIA%26%23x2019%3Bs%20AI%20Removes%20Objects%20From%20Your%20Photos%20%7C%20Two%20Minute%20Papers%20%23255%26lt%3B%5C%2Fi%26gt%3B.%20%28n.d.%29.%20Retrieved%20from%20%26lt%3Ba%20class%3D%26%23039%3Bzp-ItemURL%26%23039%3B%20href%3D%26%23039%3Bhttps%3A%5C%2F%5C%2Fwww.youtube.com%5C%2Fwatch%3Fv%3DtU484zM3pDY%26%23039%3B%26gt%3Bhttps%3A%5C%2F%5C%2Fwww.youtube.com%5C%2Fwatch%3Fv%3DtU484zM3pDY%26lt%3B%5C%2Fa%26gt%3B%26lt%3B%5C%2Fdiv%26gt%3B%5Cn%26lt%3B%5C%2Fdiv%26gt%3B%22%2C%22data%22%3A%7B%22itemType%22%3A%22videoRecording%22%2C%22title%22%3A%22NVIDIA%27s%20AI%20Removes%20Objects%20From%20Your%20Photos%20%7C%20Two%20Minute%20Papers%20%23255%22%2C%22creators%22%3A%5B%5D%2C%22abstractNote%22%3A%22Our%20Patreon%20page%20with%20the%20details%3A%20https%3A%5C%2F%5C%2Fwww.patreon.com%5C%2FTwoMinutePapers%5Cn%5CnOne-time%20payment%20links%20are%20available%20below.%20Thank%20you%20very%20much%20for%20your%20generous%20support%21%5CnPayPal%3A%20https%3A%5C%2F%5C%2Fwww.paypal.me%5C%2FTwoMinutePapers%5CnBitcoin%3A%2013hhmJnLEzwXgmgJN7RB6bWVdT7WkrFAHh%5CnEthereum%3A%200x002BB163DfE89B7aD0712846F1a1E53ba6136b5A%5CnLTC%3A%20LM8AUh5bGcNgzq6HaV1jeaJrFvmKxxgiXg%5Cn%5CnThe%20paper%20%26quot%3BImage%20Inpainting%20for%20Irregular%20Holes%20Using%20Partial%20Convolutions%26quot%3B%20is%20available%20here%3A%5Cnhttps%3A%5C%2F%5C%2Farxiv.org%5C%2Fabs%5C%2F1804.07723%5Cn%5CnWe%20would%20like%20to%20thank%20our%20generous%20Patreon%20supporters%20who%20make%20Two%20Minute%20Papers%20possible%3A%5Cn313V%2C%20Andrew%20Melnychuk%2C%20Brian%20Gilman%2C%20Christian%20Ahlin%2C%20Christoph%20Jadanowski%2C%20Dennis%20Abts%2C%20Emmanuel%2C%20Eric%20Haddad%2C%20Esa%20Turkulainen%2C%20Geronimo%20Moralez%2C%20Kjartan%20Olason%2C%20Lorin%20Atzberger%2C%20Malek%20Cellier%2C%20Marten%20Rauschenberg%2C%20Michael%20Albrecht%2C%20Michael%20Jensen%2C%20Morten%20Punnerud%20Engelstad%2C%20Nader%20Shakerin%2C%20Raul%20Ara%5Cu00fajo%20da%20Silva%2C%20Rob%20Rowe%2C%20Robin%20Graham%2C%20Ryan%20Monsurate%2C%20Shawn%20Azman%2C%20Steef%2C%20Steve%20Messina%2C%20Sunil%20Kim%2C%20Torsten%20Reil.%5Cnhttps%3A%5C%2F%5C%2Fwww.patreon.com%5C%2FTwoMinutePapers%5Cn%5CnSplash%20screen%5C%2Fthumbnail%20design%3A%20Fel%5Cu00edcia%20Feh%5Cu00e9r%20-%20http%3A%5C%2F%5C%2Ffelicia.hu%5Cn%5CnK%5Cu00e1roly%20Zsolnai-Feh%5Cu00e9r%26%23039%3Bs%20links%3A%5CnFacebook%3A%20https%3A%5C%2F%5C%2Fwww.facebook.com%5C%2FTwoMinutePap...%5CnTwitter%3A%20https%3A%5C%2F%5C%2Ftwitter.com%5C%2Fkaroly_zsolnai%5CnWeb%3A%20https%3A%5C%2F%5C%2Fcg.tuwien.ac.at%5C%2F~zsolnai%5C%2F%22%2C%22videoRecordingFormat%22%3A%22%22%2C%22studio%22%3A%22%22%2C%22date%22%3A%22%22%2C%22runningTime%22%3A%222%3A44%22%2C%22language%22%3A%22%22%2C%22ISBN%22%3A%22%22%2C%22url%22%3A%22https%3A%5C%2F%5C%2Fwww.youtube.com%5C%2Fwatch%3Fv%3DtU484zM3pDY%22%2C%22collections%22%3A%5B%224VTX49XL%22%5D%2C%22dateModified%22%3A%222020-07-22T08%3A27%3A31Z%22%7D%7D%2C%7B%22key%22%3A%22DH24YIY3%22%2C%22library%22%3A%7B%22id%22%3A295846%7D%2C%22meta%22%3A%7B%22numChildren%22%3A1%7D%2C%22bib%22%3A%22%26lt%3Bdiv%20class%3D%26quot%3Bcsl-bib-body%26quot%3B%20style%3D%26quot%3Bline-height%3A%202%3B%20padding-left%3A%202em%3B%20text-indent%3A-2em%3B%26quot%3B%26gt%3B%5Cn%20%20%26lt%3Bdiv%20class%3D%26quot%3Bcsl-entry%26quot%3B%26gt%3BMoral%20Machine.%20%28n.d.%29.%20Retrieved%20November%2013%2C%202019%2C%20from%20%26lt%3Ba%20class%3D%26%23039%3Bzp-ItemURL%26%23039%3B%20href%3D%26%23039%3Bhttp%3A%5C%2F%5C%2Fmoralmachine.mit.edu%26%23039%3B%26gt%3Bhttp%3A%5C%2F%5C%2Fmoralmachine.mit.edu%26lt%3B%5C%2Fa%26gt%3B%26lt%3B%5C%2Fdiv%26gt%3B%5Cn%26lt%3B%5C%2Fdiv%26gt%3B%22%2C%22data%22%3A%7B%22itemType%22%3A%22webpage%22%2C%22title%22%3A%22Moral%20Machine%22%2C%22creators%22%3A%5B%5D%2C%22abstractNote%22%3A%22A%20platform%20for%20public%20participation%20in%20and%20discussion%20of%20the%20human%20perspective%20on%20machine-made%20moral%20decisions%22%2C%22date%22%3A%22%22%2C%22url%22%3A%22http%3A%5C%2F%5C%2Fmoralmachine.mit.edu%22%2C%22language%22%3A%22%22%2C%22collections%22%3A%5B%224VTX49XL%22%5D%2C%22dateModified%22%3A%222020-07-22T08%3A27%3A31Z%22%7D%7D%2C%7B%22key%22%3A%22F34V5VTL%22%2C%22library%22%3A%7B%22id%22%3A295846%7D%2C%22meta%22%3A%7B%22numChildren%22%3A0%7D%2C%22bib%22%3A%22%26lt%3Bdiv%20class%3D%26quot%3Bcsl-bib-body%26quot%3B%20style%3D%26quot%3Bline-height%3A%202%3B%20padding-left%3A%202em%3B%20text-indent%3A-2em%3B%26quot%3B%26gt%3B%5Cn%20%20%26lt%3Bdiv%20class%3D%26quot%3Bcsl-entry%26quot%3B%26gt%3B%26lt%3Bi%26gt%3BThis%20AI%20Clones%20Your%20Voice%20After%20Listening%20for%205%20Seconds%20%26%23x1F910%3B%26lt%3B%5C%2Fi%26gt%3B.%20%28n.d.%29.%20Retrieved%20from%20%26lt%3Ba%20class%3D%26%23039%3Bzp-ItemURL%26%23039%3B%20href%3D%26%23039%3Bhttps%3A%5C%2F%5C%2Fwww.youtube.com%5C%2Fwatch%3Fv%3D0sR1rU3gLzQ%26%23039%3B%26gt%3Bhttps%3A%5C%2F%5C%2Fwww.youtube.com%5C%2Fwatch%3Fv%3D0sR1rU3gLzQ%26lt%3B%5C%2Fa%26gt%3B%26lt%3B%5C%2Fdiv%26gt%3B%5Cn%26lt%3B%5C%2Fdiv%26gt%3B%22%2C%22data%22%3A%7B%22itemType%22%3A%22videoRecording%22%2C%22title%22%3A%22This%20AI%20Clones%20Your%20Voice%20After%20Listening%20for%205%20Seconds%20%5Cud83e%5Cudd10%22%2C%22creators%22%3A%5B%5D%2C%22abstractNote%22%3A%22%5Cu2764%5Cufe0f%20Check%20out%20Weights%20%26amp%3B%20Biases%20here%20and%20sign%20up%20for%20a%20free%20demo%3A%20https%3A%5C%2F%5C%2Fwww.wandb.com%5C%2Fpapers%20%5Cn%5CnThe%20shown%20blog%20post%20is%20available%20here%3A%20https%3A%5C%2F%5C%2Fwww.wandb.com%5C%2Farticles%5C%2Ffundam...%5Cn%5Cn%5Cud83d%5Cudcdd%20The%20paper%20%26quot%3BTransfer%20Learning%20from%20Speaker%20Verification%20to%20Multispeaker%20Text-To-Speech%20Synthesis%26quot%3B%20and%20audio%20samples%20are%20available%20here%3A%5Cnhttps%3A%5C%2F%5C%2Farxiv.org%5C%2Fabs%5C%2F1806.04558%5Cnhttps%3A%5C%2F%5C%2Fgoogle.github.io%5C%2Ftacotron%5C%2Fpub...%5Cn%5CnAn%20unofficial%20implementation%20of%20this%20paper%20is%20available%20here.%20Note%20that%20this%20was%20not%20made%20by%20the%20authors%20of%20the%20original%20paper%20and%20may%20contain%20deviations%20from%20the%20described%20technique%20-%20please%20judge%20its%20results%20accordingly%21%20https%3A%5C%2F%5C%2Fgithub.com%5C%2FCorentinJ%5C%2FReal-Tim...%5Cn%5Cn%5Cud83d%5Cude4f%20We%20would%20like%20to%20thank%20our%20generous%20Patreon%20supporters%20who%20make%20Two%20Minute%20Papers%20possible%3A%5CnAlex%20Haro%2C%20Anastasia%20Marchenkova%2C%20Andrew%20Melnychuk%2C%20Angelos%20Evripiotis%2C%20Anthony%20Vdovitchenko%2C%20Benji%20Rabhan%2C%20Brian%20Gilman%2C%20Bryan%20Learn%2C%20Christian%20Ahlin%2C%20Claudio%20Fernandes%2C%20Daniel%20Hasegan%2C%20Dennis%20Abts%2C%20Eric%20Haddad%2C%20Eric%20Martel%2C%20Evan%20Breznyik%2C%20Geronimo%20Moralez%2C%20James%20Watt%2C%20Javier%20Bustamante%2C%20John%20De%20Witt%2C%20Kaiesh%20Vohra%2C%20Kasia%20Hayden%2C%20Kjartan%20Olason%2C%20Levente%20Szabo%2C%20Lorin%20Atzberger%2C%20Lukas%20Biewald%2C%20Marcin%20Dukaczewski%2C%20Marten%20Rauschenberg%2C%20Matthias%20Jost%2C%20Maurits%20van%20Mastrigt%2C%20Michael%20Albrecht%2C%20Michael%20Jensen%2C%20Nader%20Shakerin%2C%20Owen%20Campbell-Moore%2C%20Owen%20Skarpness%2C%20Raul%20Ara%5Cu00fajo%20da%20Silva%2C%20Rob%20Rowe%2C%20Robin%20Graham%2C%20Ryan%20Monsurate%2C%20Shawn%20Azman%2C%20Steef%2C%20Steve%20Messina%2C%20Sunil%20Kim%2C%20Taras%20Bobrovytsky%2C%20Thomas%20Krcmar%2C%20Torsten%20Reil.%5Cnhttps%3A%5C%2F%5C%2Fwww.patreon.com%5C%2FTwoMinutePapers%5Cn%5CnSplash%20screen%5C%2Fthumbnail%20design%3A%20Fel%5Cu00edcia%20Feh%5Cu00e9r%20-%20http%3A%5C%2F%5C%2Ffelicia.hu%5Cn%5CnK%5Cu00e1roly%20Zsolnai-Feh%5Cu00e9r%26%23039%3Bs%20links%3A%5CnInstagram%3A%20https%3A%5C%2F%5C%2Fwww.instagram.com%5C%2Ftwominutepa...%5CnTwitter%3A%20https%3A%5C%2F%5C%2Ftwitter.com%5C%2Fkaroly_zsolnai%5CnWeb%3A%20https%3A%5C%2F%5C%2Fcg.tuwien.ac.at%5C%2F~zsolnai%5C%2F%5Cn%5Cn%23VoiceCloning%22%2C%22videoRecordingFormat%22%3A%22%22%2C%22studio%22%3A%22%22%2C%22date%22%3A%22%22%2C%22runningTime%22%3A%225%3A30%22%2C%22language%22%3A%22%22%2C%22ISBN%22%3A%22%22%2C%22url%22%3A%22https%3A%5C%2F%5C%2Fwww.youtube.com%5C%2Fwatch%3Fv%3D0sR1rU3gLzQ%22%2C%22collections%22%3A%5B%224VTX49XL%22%5D%2C%22dateModified%22%3A%222020-07-22T08%3A27%3A31Z%22%7D%7D%2C%7B%22key%22%3A%22PNI68ST8%22%2C%22library%22%3A%7B%22id%22%3A295846%7D%2C%22meta%22%3A%7B%22numChildren%22%3A1%7D%2C%22bib%22%3A%22%26lt%3Bdiv%20class%3D%26quot%3Bcsl-bib-body%26quot%3B%20style%3D%26quot%3Bline-height%3A%202%3B%20padding-left%3A%202em%3B%20text-indent%3A-2em%3B%26quot%3B%26gt%3B%5Cn%20%20%26lt%3Bdiv%20class%3D%26quot%3Bcsl-entry%26quot%3B%26gt%3BSynthesizing%20Obama%3A%20Learning%20Lip%20Sync%20from%20Audio.%20%28n.d.%29.%20Retrieved%20November%2013%2C%202019%2C%20from%20%26lt%3Ba%20class%3D%26%23039%3Bzp-ItemURL%26%23039%3B%20href%3D%26%23039%3Bhttps%3A%5C%2F%5C%2Fgrail.cs.washington.edu%5C%2Fprojects%5C%2FAudioToObama%5C%2F%26%23039%3B%26gt%3Bhttps%3A%5C%2F%5C%2Fgrail.cs.washington.edu%5C%2Fprojects%5C%2FAudioToObama%5C%2F%26lt%3B%5C%2Fa%26gt%3B%26lt%3B%5C%2Fdiv%26gt%3B%5Cn%26lt%3B%5C%2Fdiv%26gt%3B%22%2C%22data%22%3A%7B%22itemType%22%3A%22webpage%22%2C%22title%22%3A%22Synthesizing%20Obama%3A%20Learning%20Lip%20Sync%20from%20Audio%22%2C%22creators%22%3A%5B%5D%2C%22abstractNote%22%3A%22%22%2C%22date%22%3A%22%22%2C%22url%22%3A%22https%3A%5C%2F%5C%2Fgrail.cs.washington.edu%5C%2Fprojects%5C%2FAudioToObama%5C%2F%22%2C%22language%22%3A%22%22%2C%22collections%22%3A%5B%224VTX49XL%22%5D%2C%22dateModified%22%3A%222020-07-22T08%3A27%3A31Z%22%7D%7D%2C%7B%22key%22%3A%22ESIUBCU2%22%2C%22library%22%3A%7B%22id%22%3A295846%7D%2C%22meta%22%3A%7B%22numChildren%22%3A0%7D%2C%22bib%22%3A%22%26lt%3Bdiv%20class%3D%26quot%3Bcsl-bib-body%26quot%3B%20style%3D%26quot%3Bline-height%3A%202%3B%20padding-left%3A%202em%3B%20text-indent%3A-2em%3B%26quot%3B%26gt%3B%5Cn%20%20%26lt%3Bdiv%20class%3D%26quot%3Bcsl-entry%26quot%3B%26gt%3B%26lt%3Bi%26gt%3BAudio%20To%20Obama%3A%20AI%20Learns%20Lip%20Sync%20from%20Audio%20%7C%20Two%20Minute%20Papers%20%23194%26lt%3B%5C%2Fi%26gt%3B.%20%28n.d.%29.%20Retrieved%20from%20%26lt%3Ba%20class%3D%26%23039%3Bzp-ItemURL%26%23039%3B%20href%3D%26%23039%3Bhttps%3A%5C%2F%5C%2Fwww.youtube.com%5C%2Fwatch%3Fv%3DnsuAQcvafCs%26%23039%3B%26gt%3Bhttps%3A%5C%2F%5C%2Fwww.youtube.com%5C%2Fwatch%3Fv%3DnsuAQcvafCs%26lt%3B%5C%2Fa%26gt%3B%26lt%3B%5C%2Fdiv%26gt%3B%5Cn%26lt%3B%5C%2Fdiv%26gt%3B%22%2C%22data%22%3A%7B%22itemType%22%3A%22videoRecording%22%2C%22title%22%3A%22Audio%20To%20Obama%3A%20AI%20Learns%20Lip%20Sync%20from%20Audio%20%7C%20Two%20Minute%20Papers%20%23194%22%2C%22creators%22%3A%5B%5D%2C%22abstractNote%22%3A%22The%20paper%20%26quot%3BSynthesizing%20Obama%3A%20Learning%20Lip%20Sync%20from%20Audio%26quot%3B%20is%20available%20here%3A%5Cnhttps%3A%5C%2F%5C%2Fgrail.cs.washington.edu%5C%2Fproje...%5Cn%5CnOur%20Patreon%20page%20with%20the%20details%3A%5Cnhttps%3A%5C%2F%5C%2Fwww.patreon.com%5C%2FTwoMinutePapers%5Cn%5CnPatreon%20notes%3A%5Cnhttps%3A%5C%2F%5C%2Fwww.patreon.com%5C%2FTwoMinutePape...%5Cn%5CnRecommended%20for%20you%3A%5CnWaveNet%3A%20https%3A%5C%2F%5C%2Fwww.youtube.com%5C%2Fwatch%3Fv%3DCqFIV...%5CnFace2face%3A%20https%3A%5C%2F%5C%2Fwww.youtube.com%5C%2Fwatch%3Fv%3D_S1ly...%5Cn%5CnWe%20would%20like%20to%20thank%20our%20generous%20Patreon%20supporters%20who%20make%20Two%20Minute%20Papers%20possible%3A%5CnAndrew%20Melnychuk%2C%20Brian%20Gilman%2C%20Dave%20Rushton-Smith%2C%20Dennis%20Abts%2C%20Esa%20Turkulainen%2C%20Evan%20Breznyik%2C%20Kaben%20Gabriel%20Nanlohy%2C%20Michael%20Albrecht%2C%20Michael%20Jensen%2C%20Michael%20Orenstein%2C%20Steef%2C%20Sunil%20Kim%2C%20Torsten%20Reil.%5Cnhttps%3A%5C%2F%5C%2Fwww.patreon.com%5C%2FTwoMinutePapers%5Cn%5CnTwo%20Minute%20Papers%20Merch%3A%5CnUS%3A%20http%3A%5C%2F%5C%2Ftwominutepapers.com%5C%2F%5CnEU%5C%2FWorldwide%3A%20https%3A%5C%2F%5C%2Fshop.spreadshirt.net%5C%2FTwoMinut...%5Cn%5CnMusic%3A%20Antarctica%20by%20Audionautix%20is%20licensed%20under%20a%20Creative%20Commons%20Attribution%20license%20%28https%3A%5C%2F%5C%2Fcreativecommons.org%5C%2Flicenses%5C%2F...%29%5CnArtist%3A%20http%3A%5C%2F%5C%2Faudionautix.com%5C%2F%20%5Cn%5CnThumbnail%20background%20image%20credit%3A%20https%3A%5C%2F%5C%2Fpixabay.com%5C%2Fphoto-1174489%5C%2F%5CnSplash%20screen%5C%2Fthumbnail%20design%3A%20Fel%5Cu00edcia%20Feh%5Cu00e9r%20-%20http%3A%5C%2F%5C%2Ffelicia.hu%5Cn%5CnK%5Cu00e1roly%20Zsolnai-Feh%5Cu00e9r%26%23039%3Bs%20links%3A%5CnFacebook%3A%20https%3A%5C%2F%5C%2Fwww.facebook.com%5C%2FTwoMinutePap...%5CnTwitter%3A%20https%3A%5C%2F%5C%2Ftwitter.com%5C%2Fkaroly_zsolnai%5CnWeb%3A%20https%3A%5C%2F%5C%2Fcg.tuwien.ac.at%5C%2F~zsolnai%5C%2F%5Cn%5Cn%23Deepfake%20%23Face2Face%20%23Audio2Obama%22%2C%22videoRecordingFormat%22%3A%22%22%2C%22studio%22%3A%22%22%2C%22date%22%3A%22%22%2C%22runningTime%22%3A%225%3A03%22%2C%22language%22%3A%22%22%2C%22ISBN%22%3A%22%22%2C%22url%22%3A%22https%3A%5C%2F%5C%2Fwww.youtube.com%5C%2Fwatch%3Fv%3DnsuAQcvafCs%22%2C%22collections%22%3A%5B%224VTX49XL%22%5D%2C%22dateModified%22%3A%222020-07-22T08%3A27%3A31Z%22%7D%7D%5D%7D
Heath, N. (2018). NASA’s unsung heroes: The Apollo coders who put men on the moon. Retrieved November 13, 2019, from
https://www.techrepublic.com/article/nasas-unsung-heroes-the-apollo-coders-who-put-men-on-the-moon/
Nirkin, Y., Keller, Y., & Hassner, T. (2019). FSGAN: Subject Agnostic Face Swapping and Reenactment.
ArXiv:1908.05932 [Cs] . Retrieved from
http://arxiv.org/abs/1908.05932
Károly Zsolnai-Fehér. (2019).
DeepFake Detector AIs Are Good Too! Retrieved from
https://www.youtube.com/watch?v=RoGHVI-w9bE
New Face Swapping AI Creates Amazing DeepFakes . (n.d.). Retrieved from
https://www.youtube.com/watch?v=duo-tHbSdMk
NVIDIA’s AI Removes Objects From Your Photos | Two Minute Papers #255 . (n.d.). Retrieved from
https://www.youtube.com/watch?v=tU484zM3pDY
Moral Machine. (n.d.). Retrieved November 13, 2019, from
http://moralmachine.mit.edu
This AI Clones Your Voice After Listening for 5 Seconds 🤐 . (n.d.). Retrieved from
https://www.youtube.com/watch?v=0sR1rU3gLzQ
Synthesizing Obama: Learning Lip Sync from Audio. (n.d.). Retrieved November 13, 2019, from
https://grail.cs.washington.edu/projects/AudioToObama/
Audio To Obama: AI Learns Lip Sync from Audio | Two Minute Papers #194 . (n.d.). Retrieved from
https://www.youtube.com/watch?v=nsuAQcvafCs
Post navigation